Cybersecurity, AI and Software Development | Industry and Academia Meeting – Dublin Chapter
Cybersecurity in AI and software development is becoming increasingly important as both fields are evolving rapidly and becoming integral to many industries. On Wednesday, March 12th UCD School of Computer Science and Cyber Ireland's Dublin Chapter in Collaboration with Advance Centre brought together academic and industry experts for an in-person event on Cybersecurity, AI & Software Development. Attendees were able to learn about the challenges and opportunities of Cybersecurity, AI & Software Development, how to build secure software to protect against unknown threats, and how to use AI securely in your
Key Changes to Self-Assessment Questionnaire A (SAQ A) and how these impact your organisation
The Payment Card Industry Security Standards Council (PCI SSC) announced on the 30th January 2025 significant updates to the Self-Assessment Questionnaire A (SAQ A), The latest SAQ A version is now available, but does not take effect until March 31, 2025, which is when the new PCI DSS v4.0.1 requirements become mandatory. What Are the Key Changes to SAQ A? 1) Removal of Security Requirements Originally introduced in PCI DSS v4.0 to address payment page integrity and script-based attack risks. These requirements were removed from SAQ A because fully outsourced merchants should
FAQ: Updates from PCI DSS v4.0 to PCI DSS v4.0.1
What is PCI DSS v4.0.1, and why was it introduced? PCI DSS v4.0.1 is a minor revision to PCI DSS v4.0, that clarifies requirements, corrects errors, and improves usability of the standard. These updates ensure a smoother transition for organisations working towards compliance and maintaining security best practices. The changes were made in response to feedback from industry stakeholders, including merchants, service providers, and assessors, to enhance clarity and consistency in implementing PCI DSS v4.0. What are the key changes? PCI DSS v4.0.1 does not introduce new security requirements but includes: Clarifications to existing
2024 Report on the State of Cybersecurity in the Union
The first report on the state of cybersecurity in the Union has been published by the European Union Agency for Cybersecurity (ENISA). The report provides EU policy makers with an evidence-based overview of the state of play of the cybersecurity landscape at EU, national and societal levels. It also identifies four priority areas and policy recommendations to address shortcomings and increase the level of cybersecurity across the Union. What is the ENISA Report on the State of Cybersecurity in the Union? This report provides a comprehensive overview of the cybersecurity landscape in
Free Template: Implementing the Threat Intelligence Policy in ISO 27001:2022
The Information Security Threat Intelligence Policy is required by the new ISO 27001:2022 Standard. Every organisation that needs to certify and / or transition to this standard will need to have Threat Intelligence controls in place. What is the purpose of the new Threat Intelligence Policy in ISO 27001:2022? The revisions to ISO 27001:2022 ensures this standard remains relevant to modern cybersecurity challenges. The changes address advancements in technology and the evolving threat landscape. ISO 27001:2022 mandates a proactive, intelligence-driven approach to cybersecurity. The Threat Intelligence Control (A.5.7) is integral for maintaining
Cybersecurity Skills Gap – insights from the 2024 ISC2 Cybersecurity Workforce Study
The annual ISC2 Cybersecurity Workforce Study surveyed 15,852 cyber security practitioners and decision makers to take capture the state of cybersecurity workforce and the cybersecurity skills gap. The report details the size of the workforce and the cybersecurity skills gap in meeting the demand for cybersecurity expertise. It also looks at the talent and the skills that organisations need, the wider economic context and the views of the professionals themselves. The result is a unique and thorough perspective on ecosystem that is responsible for protecting our digital world. Here are some of
Apply the Cyber Security Review Grant to secure your business
The Cyber Security Review Grant is the first of two grants launched by Enterprise Ireland and the National Cyber Security Centre (NCSC) to help Irish companies review and strengthen their security posture. Make the Cyber Security Review Grant your first/next step towards growing your business and protecting it from cyber threats. Digital tools enhance businesses capabilities to build competitive advantage and drive growth. With digital transformation comes risk and it is crucial that organisations protect sensitive information and mitigate the risk of cyber-attacks. Companies in Ireland could save 80% off a €3,000 cyber
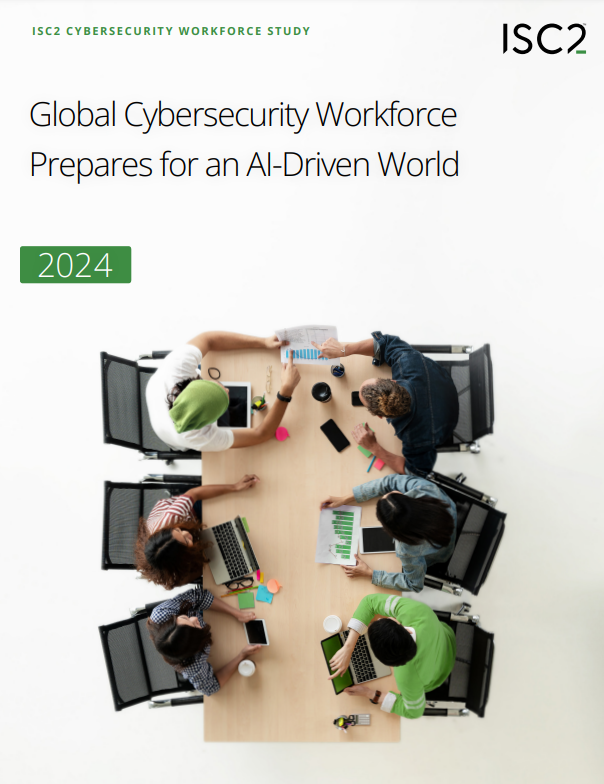
Mitigating Injection Attacks in Web Applications – A Multilayered Approach
Mitigating injection attacks requires an approach that incorporates secure coding practices at every stage of application development and deployment. Web applications have transformed how consumers and businesses interact, offering enhanced speed, convenience, and user experience. However, these benefits also introduce significant risks, as the accessibility of web applications through browsers makes them prime targets for cyberattacks. The vulnerabilities in web applications can be exploited, potentially providing attackers with access to sensitive personal and financial data. According to the 2024 Verizon Data Breach Investigations Report, web applications held the top spot as
Threat Modeling Workshop at ISC2 Security Congress – Las Vegas, October 12 and 13, 2024
Building applications for an ever-changing threat landscape is critical and challenging. Join Fabio Cerullo at the ISC2 Security Congress in Las Vegas for a highly interactive Threat Modeling workshop and learn how to build resilient web applications. Threat Modeling Workshops are scheduled for the two days before ISC2 Security Congress 2024 officially opens – Saturday, October 12 and Sunday, October 13. The workshop combines theory review and a strong emphasis on practical exercises. Participants on the Threat Modeling Workshop will learn how to: Integrate threat modeling into the application development life cycle Apply
OWASP 2024 Global AppSec San Francisco (Sept 23-27)
Web application vulnerabilities can be exploited to access critical and confidential data. Join Fabio Cerullo at OWASP 2024 Global AppSec San Francisco for a highly interactive session on Web Application Security Essentials Web applications play a key role in the success of an organisation, from streamlining business processes to creating online interactions that ensure a positive customer experience. However, web applications do allow access to critical and confidential resources. But, without understanding web application vulnerabilities and addressing them, organisations risk their data, their operations and their reputation. At OWASP 2024 Global