Apply the Cyber Security Review Grant to secure your business
The Cyber Security Review Grant is the first of two grants launched by Enterprise Ireland and the National Cyber Security Centre (NCSC) to help Irish companies review and strengthen their security posture. Make the Cyber Security Review Grant your first/next step towards growing your business and protecting it from cyber threats. Digital tools enhance businesses capabilities to build competitive advantage and drive growth. With digital transformation comes risk and it is crucial that organisations protect sensitive information and mitigate the risk of cyber-attacks. Companies in Ireland could save 80% off a €3,000 cyber
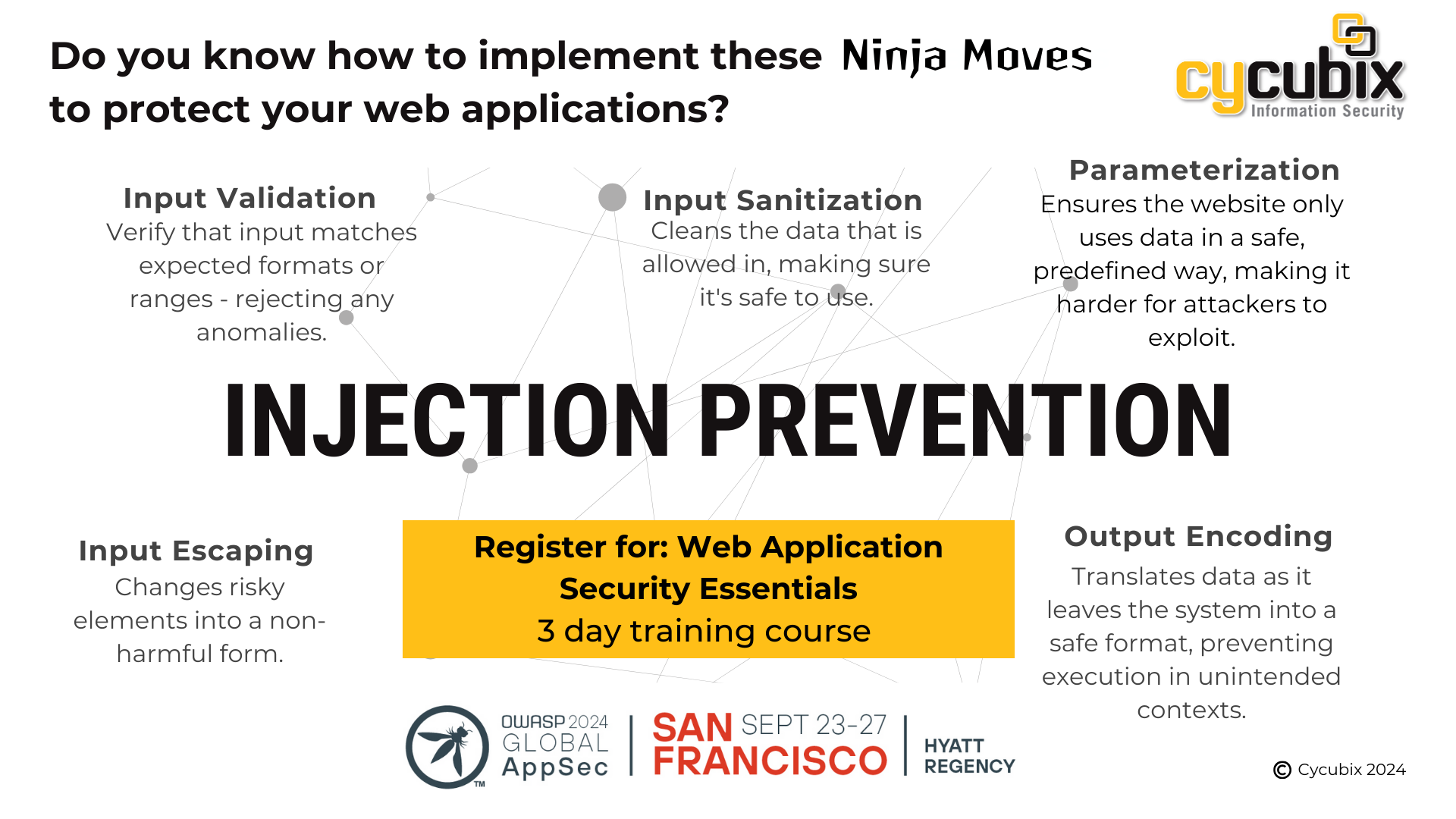
Mitigating Injection Attacks in Web Applications – A Multilayered Approach
Mitigating injection attacks requires an approach that incorporates secure coding practices at every stage of application development and deployment. Web applications have transformed how consumers and businesses interact, offering enhanced speed, convenience, and user experience. However, these benefits also introduce significant risks, as the accessibility of web applications through browsers makes them prime targets for cyberattacks. The vulnerabilities in web applications can be exploited, potentially providing attackers with access to sensitive personal and financial data. According to the 2024 Verizon Data Breach Investigations Report, web applications held the top spot as
Navigating the NIS2 Directive: Strengthening Cybersecurity Across the EU
The NIS2 Directive takes a significant step towards enhancing cybersecurity across the European Union. Designed to address the evolving threat landscape and ensure a robust, unified approach to cybersecurity, the regulations impose stricter security requirements and reporting obligations on organisations that provide essential services and critical infrastructure . What is the NIS2 Directive? The NIS2 Directive is a set of EU-wide cybersecurity requirements and regulations designed to increase the cybersecurity preparedness of EU member states. Organisations that provide essential services, digital service providers, suppliers of critical technologies, and public administration entities will
Threat Modeling Workshop at ISC2 Security Congress – Las Vegas, October 12 and 13, 2024
Building applications for an ever-changing threat landscape is critical and challenging. Join Fabio Cerullo at the ISC2 Security Congress in Las Vegas for a highly interactive Threat Modeling workshop and learn how to build resilient web applications. Threat Modeling Workshops are scheduled for the two days before ISC2 Security Congress 2024 officially opens – Saturday, October 12 and Sunday, October 13. The workshop combines theory review and a strong emphasis on practical exercises. Participants on the Threat Modeling Workshop will learn how to: Integrate threat modeling into the application development life cycle Apply
OWASP 2024 Global AppSec San Francisco (Sept 23-27)
Web application vulnerabilities can be exploited to access critical and confidential data. Join Fabio Cerullo at OWASP 2024 Global AppSec San Francisco for a highly interactive session on Web Application Security Essentials Web applications play a key role in the success of an organisation, from streamlining business processes to creating online interactions that ensure a positive customer experience. However, web applications do allow access to critical and confidential resources. But, without understanding web application vulnerabilities and addressing them, organisations risk their data, their operations and their reputation. At OWASP 2024 Global
How to Utilise the European Cybersecurity Skills Framework by ENISA to Bridge the Cybersecurity Skills Gap
The demand for skilled cybersecurity professionals continues to grow in response to increased reliance on technology matched by a steady rise in cybercrime. The European Cybersecurity Skills Framework (ECSF) - developed by ENISA (The European Union Agency for Cybersecurity) establishes a common understanding of the roles, competencies, skills, and knowledge required in the cybersecurity field. Why the European Cybersecurity Skills Framework is important The ECSF provides a structured approach to defining and recognising cybersecurity skills, helping individuals to effectively manage their professional development and career paths. By aligning certification credentials with professional roles,
Why Prepare for ISC2 Certifications with an Official Training Partner
Companies rely on ISC2-certified professionals to prepare for and recover from cyberattacks. ISC2 certifications are recognised as the gold standard in the industry and demonstrate comprehensive and professional knowledge critical to developing and protecting systems and data. With ISC2 certifications so highly regarded in the cybersecurity industry, there is no shortage of training companies that offer preparation for the ISC2 certification exam. Not all of these are affiliated with ISC2. It is important to know who you’re partnering with and understand the benefits of engaging an ISC2 Official Training Partner. As an
SSCP Domain Update FAQ
On September 15, 2024, ISC2 will update the Systems Security Certified Practitioner (SSCP) credential exam. These SSCP Domain updates are the result of the Job Task Analysis (JTA), which is an analysis of the current content of the credential evaluated by ISC2 members on a triennial cycle. A title change is occurring for Domain 1. Security Operations and Administration will have a new title of Security Concepts and Practices. Q: Why are changes being made to the SSCP exam? ISC2 has an obligation to its membership to maintain the relevancy of its credentials. These enhancements
CISSP Computerized Adaptive Testing
ISC2 has introduced Computerized Adaptive Testing for CISSP exams. Based on the same exam content outline as the linear, fixed-form exam, CISSP Computerized Adaptive Testing (CAT) is a more precise and efficient evaluation of your competency. CISSP CAT enables you to prove your knowledge by answering fewer items and completing the exam in half the time. How Does it Work? “Each candidate taking the CISSP CAT exam will start with an item that is well below the passing standard. Following a candidate's response to an item, the scoring algorithm re-estimates the candidate's
Celebrating 30 Years of CISSP
ISC2 Celebrates 30th Anniversary of CISSP Certification Launched in 1994, CISSP certification is now held by more than 165,000 practitioners globally and remains the most sought-after in the field for cyber leaders. Since its inception, the CISSP has been recognized as the “gold standard” in cybersecurity, with recognition by governments and accredited to standards of international bodies, including the International Organization for Standardization (ISO), the U.S. Department of Defense (DoD) and the U.K National Academic Recognition Information Centre. Established in 1994, the class of CISSP-holders around the world has risen from 46